QUOTE(syahpian @ May 30 2025, 09:35 PM)
Only SFP Port is 2.5G,not really useful actually.Since most people dont really use SFP port.
Unless there is another 2.5G Lan or more then more suitable for current speed technology.
Enterprise Networking Mikrotik Routers (RouterBoard & RouterOS), User and owner discussion group
|
|
 May 31 2025, 04:51 PM May 31 2025, 04:51 PM
Show posts by this member only | IPv6 | Post
#3301
|
     
Senior Member
1,882 posts Joined: Sep 2017 |
|
|
|
|
|
|
 May 31 2025, 06:31 PM May 31 2025, 06:31 PM
|
     
Senior Member
1,209 posts Joined: Aug 2018 |
QUOTE(syahpian @ May 30 2025, 09:35 PM) Anybody who want to buy this, keep in mind:1. The spec sheet is wrong. It uses a very rare 32-bit ARM CPU, same like hex refresh. 2. Read the block diagram. SPF and LAN1 are both dedicated port to the CPU. Meaning if you do switching on them, they will be processed by the CPU instead of switch chip. So for optimal performance, LAN2 - LAN5 should be used for switching while SPF + LAN1 should be used exclusively for routing. The same is true for LAN1 on hex refresh. 3. No L3 Hardware Offload at all. Other than that, this thing looks good. The use case is niche but considering the price, it is great. Example: Your house isn't big. Your internet speed is 1G or less but you want to use PON stick. You also have one PoE out port for WiFi allowing optimal position. |
|
|
 Jun 1 2025, 12:51 PM Jun 1 2025, 12:51 PM
|
     
Senior Member
1,459 posts Joined: Sep 2021 |
i waiting Mikrotik new launch like RB5009 or high end all port must be 2.5GE Port all imported seen almost delay product launch new
|
|
|
 Jun 1 2025, 05:12 PM Jun 1 2025, 05:12 PM
|
   
Junior Member
586 posts Joined: Mar 2006 |
Hi kwss, I'm new to Mikrotik products.
I'm using two D-LINK DIR-X3000Z for mesh now. I would like to get one Mikrotik router as the router gateway and turn the two D-LINK as APs. Here are my goals: 1. Isolate Android TV box (wired) and IoT devices (wireless) from my PC and Raspberry Pi. 2. Configure all devices to access Pi-hole via the Raspberry Pi. 3. Restrict the Android TV box to only access Pi-hole and Jellyfin on the Raspberry Pi. 4. Optimize and reduce latency for PC gaming while family members streaming video. 5. Implement basic firewall rules to block unsolicited WAN access to my LAN. ether1 - WAN (500Mbps) ether2 - PC ether3 - Raspberry Pi ether4 - D-LINK AP1 ether5 - D-LINK AP2 Between the hAP ax2 and hAP ax3, which one do you recommend? Will the ax2 overheat without air conditioning? Room temperature 32'c. Is the ax3 sufficient, or should I save more money and opt for the RB5009? This post has been edited by Kadaj: Jun 1 2025, 05:15 PM |
|
|
 Jun 1 2025, 05:31 PM Jun 1 2025, 05:31 PM
Show posts by this member only | IPv6 | Post
#3305
|
   
Junior Member
612 posts Joined: Apr 2005 From: http://127.0.0.1:80/announce |
QUOTE(Kadaj @ Jun 1 2025, 05:12 PM) Between the hAP ax2 and hAP ax3, which one do you recommend? Got budget, go for rb5009. I came from ac2, bought rb5009. feels like overkill for my small simple homelab. sold it to my office and bought ax3. happy with it but need to fine-tune the wifi1 (5G) frequency that suites ur needs.Will the ax2 overheat without air conditioning? Room temperature 32'c. Is the ax3 sufficient, or should I save more money and opt for the RB5009? |
|
|
 Jun 1 2025, 09:59 PM Jun 1 2025, 09:59 PM
Show posts by this member only | IPv6 | Post
#3306
|
     
Senior Member
1,209 posts Joined: Aug 2018 |
QUOTE(Kadaj @ Jun 1 2025, 05:12 PM) Hi kwss, I'm new to Mikrotik products. I will go with hap ax3 unless your budget is constrained.I'm using two D-LINK DIR-X3000Z for mesh now. I would like to get one Mikrotik router as the router gateway and turn the two D-LINK as APs. Here are my goals: 1. Isolate Android TV box (wired) and IoT devices (wireless) from my PC and Raspberry Pi. 2. Configure all devices to access Pi-hole via the Raspberry Pi. 3. Restrict the Android TV box to only access Pi-hole and Jellyfin on the Raspberry Pi. 4. Optimize and reduce latency for PC gaming while family members streaming video. 5. Implement basic firewall rules to block unsolicited WAN access to my LAN. ether1 - WAN (500Mbps) ether2 - PC ether3 - Raspberry Pi ether4 - D-LINK AP1 ether5 - D-LINK AP2 Between the hAP ax2 and hAP ax3, which one do you recommend? Will the ax2 overheat without air conditioning? Room temperature 32'c. Is the ax3 sufficient, or should I save more money and opt for the RB5009? In fact I will actively discourage people from buying hap ax2. The reason is the ax2 is rigged. Both uses the exact same SoC but I suspect due to the smaller chassis, there's thermal problem. Mikrotik limit the SoC frequency on ax2 so you are buying hardware that you cannot use to it's full potential. Whether the discount justify the performance drop is a very personal preference. Ax3 also gives you one 2.5g port and higher gain 5ghz antenna. You need to consider if those are thing you consider important or totally irrelevant. Ax3 also has a higher RouterOS license level but for home use that's irrelevant. Ax2 has a higher gain 2.4ghz antenna. If your IoT is 2.4ghz then this might be a consideration. To answer your goals. Do you intent to use your hap ax wifi as well or you only want to stick to your mesh? Things are not so straightforward when it comes to isolating devices. Your wifi need to be able to segment those IoT device to a different network, via a different SSID to a different VLAN that Mikrotik can act against. Easiest is to connect all you IoT to the Mikrotik wifi. Continue to use your mesh for non-isolated devices. When you say you want to isolate your wired TV box but I don't see it in your diagram. You must connect it directly to Mikrotik for it to be isolated. Isolation by IP address is not security as attacker can change IP. Plus your layer 2 network is still visible to attacker. You can change your DHCP server setting and point to Pi-Hole. If you want to restrict Android TV to only be able to communicate with your Pi, then you need to have the port connected to your Pi to act as different network as well. In the Interface List, configure all the ports accordingly so you can just use the list in firewall configuration. You get an advantage no layer 2 attack can hit your Pi, from any network. I am going to tell you the truth, there's nothing specific to optimize for gaming. Just configure EIM-NAT, enable UPnP for your game to open port. That's all. Traffic QoS are not effective in my opinion. They only work when your own network is congested. It won't help you when TM is congested. Doing QoS also effectively disable FastTrack so all your packet route slower. You also need QoS processing, which isn't free, all of them increases latency. Lately, QoS only affect transmit. You cannot control in which order TM sends you traffic or how their HQoS prioritize your packet. Mikrotik default firewall rules already did all that, for both IPv4 and IPv6. Final note: TM only give you one IPv6 subnet. So you need to choose which network to have it. All other network cannot have IPv6 GUA. In this case, I think your PC and non-isolated wifi device will be on the same network, hence this is the one you use IPv6. Configuration wise is another big topic. Either using VLAN, use routed port, do a hybrid. That's up to you Most secure and reliable is just use routed port. It won't introduce network loop, it won't allow broadcast storm to propagate.Less overhead. No 4094 network limit. The cons is you must buy layer 3 managed switch if you decide to use one later. Not only that, you have to consider which routing protocol to use. OSPF is a common one. The reason is many big player charge extra for switch to do BGP. If you stay in Mikrotik ecosystem, this is irrelevant as Mikrotik do everything. |
|
|
|
|
|
 Jun 3 2025, 09:40 PM Jun 3 2025, 09:40 PM
|
   
Junior Member
586 posts Joined: Mar 2006 |
kwss
AX3 seems more suitable for a home setup. QUOTE Easiest is to connect all you IoT to the Mikrotik wifi. Continue to use your mesh for non-isolated devices. I think this is the easiest way for wifi setup. QUOTE When you say you want to isolate your wired TV box but I don't see it in your diagram. You must connect it directly to Mikrotik for it to be isolated. Isolation by IP address is not security as attacker can change IP. Plus your layer 2 network is still visible to attacker. ether4 - D-LINK AP1 (1st floor) ether5 - D-LINK AP2 (Ground floor, TV Box) I have pulled an Ethernet cable from the router (1st floor) to the ground floor, so the two APs serve different floors. LAN1 = ether1 + ether2 LAN2 = ether3 + ether4 1. Create Bridges for LAN1 and LAN2 2. Add Ports to Bridges 3. Assign IP Subnets to Each Bridge 4. Setup DHCP Servers for Both Networks 5. Create Interface Lists (Optional) 6. Set Firewall Rules to Block Cross-Traffic Maybe this will be my setup for now. Till I get a managed switch then I can create vlan for more granular isolation next time right? I thought QoS was very useful coz every time I saw someone mention it when I was looking for gaming optimization. You're right, our issue is TM congestion especially at night. Anyway I don't play FPS so I'm fine. Just trying to see what else the MikroTik router can do. ahlong I think RB5009 overkill for most people like us. So are you happy with ax3? This post has been edited by Kadaj: Jun 4 2025, 11:21 AM |
|
|
 Jun 3 2025, 11:17 PM Jun 3 2025, 11:17 PM
Show posts by this member only | IPv6 | Post
#3308
|
   
Junior Member
612 posts Joined: Apr 2005 From: http://127.0.0.1:80/announce |
QUOTE(Kadaj @ Jun 3 2025, 09:40 PM) only with wifibut slowly got nice setup for it overall, its mikrotik! Kadaj liked this post
|
|
|
 Jun 4 2025, 01:32 PM Jun 4 2025, 01:32 PM
Show posts by this member only | IPv6 | Post
#3309
|
     
Senior Member
1,209 posts Joined: Aug 2018 |
QUOTE(Kadaj @ Jun 3 2025, 09:40 PM) kwss On high level those looks correct.AX3 seems more suitable for a home setup. I think this is the easiest way for wifi setup. ether4 - D-LINK AP1 (1st floor) ether5 - D-LINK AP2 (Ground floor, TV Box) I have pulled an Ethernet cable from the router (1st floor) to the ground floor, so the two APs serve different floors. LAN1 = ether1 + ether2 LAN2 = ether3 + ether4 1. Create Bridges for LAN1 and LAN2 2. Add Ports to Bridges 3. Assign IP Subnets to Each Bridge 4. Setup DHCP Servers for Both Networks 5. Create Interface Lists (Optional) 6. Set Firewall Rules to Block Cross-Traffic Maybe this will be my setup for now. Till I get a managed switch then I can create vlan for more granular isolation next time right? I thought QoS was very useful coz every time I saw someone mention it when I was looking for gaming optimization. You're right, our issue is TM congestion especially at night. Anyway I don't play FPS so I'm fine. Just trying to see what else the MikroTik router can do. ahlong I think RB5009 overkill for most people like us. So are you happy with ax3? I highly recommend using Interface List because it will make your firewall rules easier to manage and less error prone. It also makes them easier to read, kind of self-documented. If you use VLAN, you only need a L2 switch that can do VLAN. If you use routed port, you need a managed L3 switch. Either way a dumb switch won't work. OK to add here... Since you are home user, you can just use static route instead of routing protocol as suggested from my previous post. I am sure you won't have more than 20 networks at home. QoS only works if your own network upload is pegged or congested. It will otherwise not work. You will have better luck trying different VPN server till you get an uncongested circuit. Kadaj liked this post
|
|
|
 Jun 6 2025, 03:02 PM Jun 6 2025, 03:02 PM
|
    
Senior Member
857 posts Joined: Oct 2009 |
Greeting Sifus,
Am recently researching into running a IKEv2 VPN server for site-to-site and also for my android device to connect back to home network However was not able to ping or reach public IP port UDP 500 & 4500 from the Internet even with all firewall filter deny rules temporarily disabled. With further digging I suspected CG-NAT? As the PPPoE link was on address 100.x.x.x but my public IP was 161.x.x.x Any suggestions whether I should try to request for a public IP from TIME Internet, or we have reached the point where IPv6 makes sense now? |
|
|
 Jun 6 2025, 06:26 PM Jun 6 2025, 06:26 PM
Show posts by this member only | IPv6 | Post
#3311
|
     
Senior Member
1,209 posts Joined: Aug 2018 |
QUOTE(winter01942 @ Jun 6 2025, 03:02 PM) Greeting Sifus, I would skip IKEv2 and use Wireguard on IPv6 instead.Am recently researching into running a IKEv2 VPN server for site-to-site and also for my android device to connect back to home network However was not able to ping or reach public IP port UDP 500 & 4500 from the Internet even with all firewall filter deny rules temporarily disabled. With further digging I suspected CG-NAT? As the PPPoE link was on address 100.x.x.x but my public IP was 161.x.x.x Any suggestions whether I should try to request for a public IP from TIME Internet, or we have reached the point where IPv6 makes sense now? It works on more network. It saves battery since you no longer need keep alive to maintain NAT session. I never turn off my Wireguard on phone and didn't get faster battery drain due to this one single change. Option 1: Use a DDNS provider like freedns.afraid.org. Create a script to open the link. Call the script from DHCPv6 client whenever the DCHP pool is updated. Wireguard server runs on Mikrotik. Option 2: Can use Mikrotik DDNS but I never try this before since I already have a very elaborated setup before they introduce this feature. If you just connect back to share file, Mikrotik Back To Home is just an app that abstract everything for very easy setup. Option 3: If you have a VPS anywhere, let that act as a Wireguard hub and everything else act as a spoke. Benefit of this is low latency and you don't need to deal with the host of problem that comes with dynamic IPv6 prefix that infest TM. You do need to configure each network manually in the Wireguard config. Alternatively you can use orchestration tool like NetBird to help if you have a lot of spokes with a lot of network. Option 4: Use SaaS like Tailscale. Technically they are a Option 3 but it's their server instead of your server. I never like setting my own VPN just to use third party service so I build Option 3 personally. Choose your own option, don't have to follow me. |
|
|
 Jun 7 2025, 12:11 AM Jun 7 2025, 12:11 AM
|
    
Senior Member
857 posts Joined: Oct 2009 |
QUOTE(kwss @ Jun 6 2025, 06:26 PM) I would skip IKEv2 and use Wireguard on IPv6 instead. Thanks for the advice, I did previously use the built-in Back To Home functionality, and while it works, it was really slow.It works on more network. It saves battery since you no longer need keep alive to maintain NAT session. I never turn off my Wireguard on phone and didn't get faster battery drain due to this one single change. » Click to show Spoiler - click again to hide... « Maybe I could give it another go manually and see how that works out. I am currently using Mikrotik DDNS and just pointing my own domain CNAME to it. |
|
|
 Jun 7 2025, 12:36 AM Jun 7 2025, 12:36 AM
|
   
Junior Member
586 posts Joined: Mar 2006 |
ahlong I should get a mikrotik too, it's so powerful! kwss Thanks!! I've learned a lot from you. Appreciate! winter01942 I recommend Wireguard too. It's very fast and easy to setup by using script. kwss liked this post
|
|
|
|
|
|
 Jun 7 2025, 12:48 AM Jun 7 2025, 12:48 AM
Show posts by this member only | IPv6 | Post
#3314
|
     
Senior Member
1,209 posts Joined: Aug 2018 |
QUOTE(winter01942 @ Jun 7 2025, 12:11 AM) Thanks for the advice, I did previously use the built-in Back To Home functionality, and while it works, it was really slow. It's show because behind the scene it's wireguard inside another wireguard tunnel back to Mikrotik server in Latvia. That's how they workaround CGNAT.Maybe I could give it another go manually and see how that works out. I am currently using Mikrotik DDNS and just pointing my own domain CNAME to it. Tailscale is slow for the same reason. If you can just use Mikrotik DDNS but directly wireguard to your router over IPv6, performance should be top notch. |
|
|
 Jun 12 2025, 03:20 PM Jun 12 2025, 03:20 PM
Show posts by this member only | IPv6 | Post
#3315
|
    
Junior Member
818 posts Joined: Jul 2008 From: Kota Kinabalu <-> Kuala Lumpur |
jusbella liked this post
|
|
|
 Jun 12 2025, 03:43 PM Jun 12 2025, 03:43 PM
Show posts by this member only | IPv6 | Post
#3316
|
     
Senior Member
1,209 posts Joined: Aug 2018 |
|
|
|
 Jun 12 2025, 03:50 PM Jun 12 2025, 03:50 PM
Show posts by this member only | IPv6 | Post
#3317
|
    
Junior Member
818 posts Joined: Jul 2008 From: Kota Kinabalu <-> Kuala Lumpur |
QUOTE(kwss @ Jun 12 2025, 03:43 PM) Mikrotik didn't fix anything. TM made some changes for your BNG. really? cause using back 7.19.1 stable it revert back to 1480 Mine still cannot do 1492. If Mikrotik truly fix it then it should be able to do 1500 or whatever number you put in it. 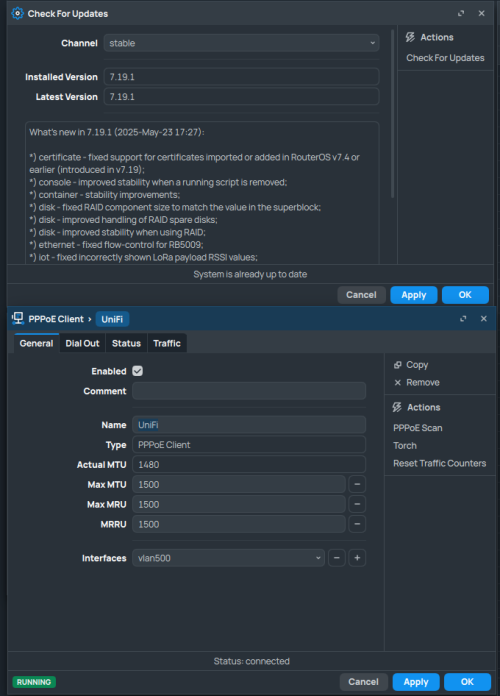 7.20beta2 (same setting) 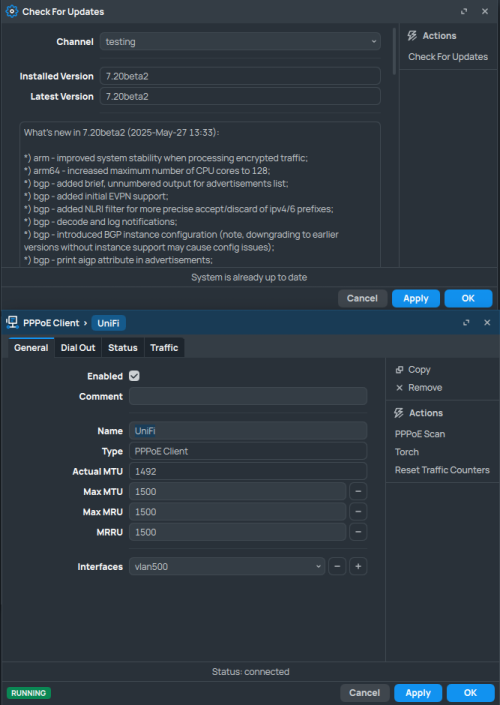 This post has been edited by syahpian: Jun 12 2025, 03:55 PM |
|
|
 Jun 12 2025, 03:55 PM Jun 12 2025, 03:55 PM
Show posts by this member only | IPv6 | Post
#3318
|
     
Senior Member
1,209 posts Joined: Aug 2018 |
QUOTE(syahpian @ Jun 12 2025, 03:50 PM) Yes. Confirm not working for me. Tested it 2x with 1500 and 1492 when 7.20b2 just release. Tested it again when read your post. Tested again before replying this post. What's your location? |
|
|
 Jun 12 2025, 03:57 PM Jun 12 2025, 03:57 PM
|
    
Junior Member
818 posts Joined: Jul 2008 From: Kota Kinabalu <-> Kuala Lumpur |
|
|
|
 Jun 12 2025, 04:20 PM Jun 12 2025, 04:20 PM
Show posts by this member only | IPv6 | Post
#3320
|
     
Senior Member
1,209 posts Joined: Aug 2018 |
syahpian liked this post
|
| Change to: |  0.0178sec 0.0178sec
 1.23 1.23
 6 queries 6 queries
 GZIP Disabled GZIP Disabled
Time is now: 24th December 2025 - 01:34 PM |