
QUOTE(jjj2 @ Apr 5 2018, 12:56 PM)
Hi Guys,
For your convenience, please kindly proceed to https://modification.time.com.my
if you want to modify the followings :
1) Amend / Add-on Call Forwarding/Call Divert feature
2) Change your TIME Home Voice Number (Eg. 03-5039 xxxx / 04-293 xxxx)
3) Upgrade or Downgrade your TIME Home Voice package
4) Merge/Split your existing accounts
5) Relocation (Indoor/Outdoor)
For more details, please kindly contact Customer Service @ 1800 18 1818 .
Thanks.
For your convenience, please kindly proceed to https://modification.time.com.my
if you want to modify the followings :
1) Amend / Add-on Call Forwarding/Call Divert feature
2) Change your TIME Home Voice Number (Eg. 03-5039 xxxx / 04-293 xxxx)
3) Upgrade or Downgrade your TIME Home Voice package
4) Merge/Split your existing accounts
5) Relocation (Indoor/Outdoor)
For more details, please kindly contact Customer Service @ 1800 18 1818 .
Thanks.
QUOTE(jjj2 @ Sep 23 2017, 09:12 AM)
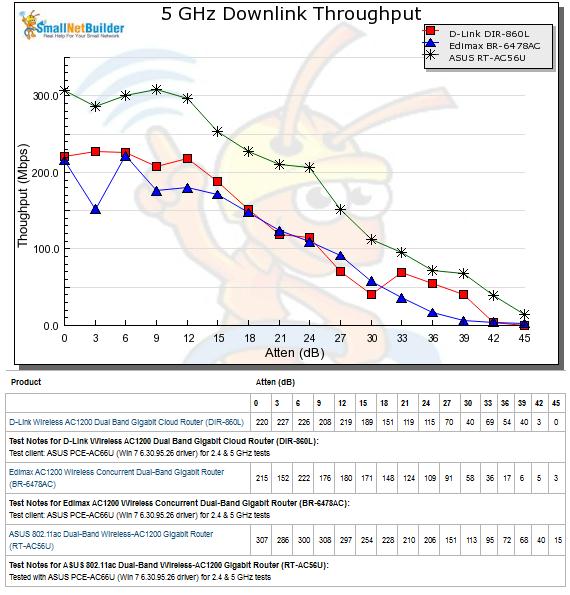
D-LINK DIR850L ROUTER -- FIRMWARE AVAILABLE FOR DOWNLOAD (PATCHING ZERO DAY FLAWS)
DOWNLOAD HERE
NOTE :
--- Please first upgrade the Router with the transitional firmware, DIR-850L Bx_FW208SGb01
--- And proceed with the DIR-850L Bx_FW210SGb01 firmware upgrade
*Please read the enclosed DIR-850L HW B Firmware upgrade guide .
Problems Resolved:
Fixed the security issues reported by Researcher Pierre Kim on Sep 8th, 2017.
• Firmware Protection
• WAN && LAN - Retrieving admin password, gaining full access using the custom mydlink Cloud protocol (CVE-2017-14417, CVE-2017-14418)
• WAN - Weak Cloud protocol (CVE-2017-14419, CVE-2017-14420)
• LAN - Backdoor access (CVE-2017-14421)
• WAN && LAN - Stunnel private keys (CVE-2017-14422)
• Local - Weak files permission and credentials stored in clear text
(CVE-2017-14424, CVE-2017-14425, CVE-2017-14426, CVE-2017-14427, CVE-2017-14428)
• WAN - Pre-Auth RCEs as root (L2)
(CVE-2017-14429)
• LAN - DoS attack against some daemons (CVE-2017-14430)
SUMMARY OF PREVIOUS 0-DAY FLAWS FOUND ON DLINK DIR850L ROUTER (RevA & RevB)
1) Weak or NO protection on Firmware.
2) Weak File permissions are stored in clear text.
3) Cross-site scriting flaws which enables attacker to steal the authentication cookies.
4) Vulnerabilities in MyDLink cloud protocol enables attacker to gain full access to the Router.
5) RevB backdoor access.
6) Hardcoded private keys in the firmware RevA & RevB enables MiTM attcks.
7) DNS Hijack on RevA.
8) Vulnerabilities in RevB enables command injection attacks.
9) DOS flaws in some daemons running in both RevA & RevB can be crashed via LAN.
* If you would like to wait for Telco-specific firmware, suggest you to wait for their own release. The above upgrade & patch has been tested on v2.07TT firmware by my team & it works fine.
DOWNLOAD HERE
NOTE :
--- Please first upgrade the Router with the transitional firmware, DIR-850L Bx_FW208SGb01
--- And proceed with the DIR-850L Bx_FW210SGb01 firmware upgrade
*Please read the enclosed DIR-850L HW B Firmware upgrade guide .
Problems Resolved:
Fixed the security issues reported by Researcher Pierre Kim on Sep 8th, 2017.
• Firmware Protection
• WAN && LAN - Retrieving admin password, gaining full access using the custom mydlink Cloud protocol (CVE-2017-14417, CVE-2017-14418)
• WAN - Weak Cloud protocol (CVE-2017-14419, CVE-2017-14420)
• LAN - Backdoor access (CVE-2017-14421)
• WAN && LAN - Stunnel private keys (CVE-2017-14422)
• Local - Weak files permission and credentials stored in clear text
(CVE-2017-14424, CVE-2017-14425, CVE-2017-14426, CVE-2017-14427, CVE-2017-14428)
• WAN - Pre-Auth RCEs as root (L2)
(CVE-2017-14429)
• LAN - DoS attack against some daemons (CVE-2017-14430)
SUMMARY OF PREVIOUS 0-DAY FLAWS FOUND ON DLINK DIR850L ROUTER (RevA & RevB)
1) Weak or NO protection on Firmware.
2) Weak File permissions are stored in clear text.
3) Cross-site scriting flaws which enables attacker to steal the authentication cookies.
4) Vulnerabilities in MyDLink cloud protocol enables attacker to gain full access to the Router.
5) RevB backdoor access.
6) Hardcoded private keys in the firmware RevA & RevB enables MiTM attcks.
7) DNS Hijack on RevA.
8) Vulnerabilities in RevB enables command injection attacks.
9) DOS flaws in some daemons running in both RevA & RevB can be crashed via LAN.
* If you would like to wait for Telco-specific firmware, suggest you to wait for their own release. The above upgrade & patch has been tested on v2.07TT firmware by my team & it works fine.
QUOTE(jjj2 @ Dec 24 2015, 06:14 AM)
Hi Bro,
For sure at this moment any p2p traffic is Not blocked.
But you have reasons to believe some forms of traffic shaping is happening.
This is what happened to other ISP like TM as well.
But one of the easy way to bypass is to alter your computer/Router/any pppoe dialing device's DNS.
Commonly used Public DNS are Google & OpenDNS :
There are 2 Ways to change your DNS,
I) Via Router Configurations
You can access the Router by default 192.168.1.1 or 192.168.0.1 (Assuming it's not changed).
Feel Free PM me if you need the standard login credentials for Time Routers.
II) Via Network Adapters.
Please refer this Step by Step guideline.
Google DNS https://developers.google.com/speed/public-dns/docs/using
OpenDNS https://use.opendns.com/
We have a tool to detect whether the ISP is actually shaping your traffic.
Feel free to PM me should you need that.
Thanks.
For sure at this moment any p2p traffic is Not blocked.
But you have reasons to believe some forms of traffic shaping is happening.
This is what happened to other ISP like TM as well.
But one of the easy way to bypass is to alter your computer/Router/any pppoe dialing device's DNS.
Commonly used Public DNS are Google & OpenDNS :
There are 2 Ways to change your DNS,
I) Via Router Configurations
You can access the Router by default 192.168.1.1 or 192.168.0.1 (Assuming it's not changed).
Feel Free PM me if you need the standard login credentials for Time Routers.
II) Via Network Adapters.
Please refer this Step by Step guideline.
Google DNS https://developers.google.com/speed/public-dns/docs/using
OpenDNS https://use.opendns.com/
We have a tool to detect whether the ISP is actually shaping your traffic.
Feel free to PM me should you need that.
Thanks.
QUOTE(jjj2 @ Dec 24 2015, 06:14 AM)
FEEDBACK & REPORT NEEDED
Dear All FTTX Users,
Lately there has been quite a number of cases reported that carry the following symptoms :
1) Slow Download, Fast Upload
Happens mostly at night hours.
2) Speed Test to local servers are fine, but when performing actual downloads, speed is far far more slower that it should at least be.
Please kindly provide the following info :
1) Screenshots of Speedtest,TraceRoute results or any related evidences.
2) Account No / Service No of yours.
In order to provide satisfactory services to all valuable customers & users, as a full service pioneer team, we are striving our best to assist you all in every possible aspect, your priceless feedbacks are very much appreciated.
Feel free to pm or email us should you require further assistance.
HistoryDear All FTTX Users,
Lately there has been quite a number of cases reported that carry the following symptoms :
1) Slow Download, Fast Upload
Happens mostly at night hours.
2) Speed Test to local servers are fine, but when performing actual downloads, speed is far far more slower that it should at least be.
Please kindly provide the following info :
1) Screenshots of Speedtest,TraceRoute results or any related evidences.
2) Account No / Service No of yours.
In order to provide satisfactory services to all valuable customers & users, as a full service pioneer team, we are striving our best to assist you all in every possible aspect, your priceless feedbacks are very much appreciated.
Feel free to pm or email us should you require further assistance.
v1 - https://forum.lowyat.net/topic/2189931
v2 - https://forum.lowyat.net/topic/3247871
This post has been edited by ezinger: Apr 12 2018, 11:38 PM


 Apr 4 2016, 11:45 PM, updated 8y ago
Apr 4 2016, 11:45 PM, updated 8y ago

 Quote
Quote









 0.0344sec
0.0344sec
 0.42
0.42
 7 queries
7 queries
 GZIP Disabled
GZIP Disabled