QUOTE(kwss @ Jan 7 2024, 01:03 AM)
CODE
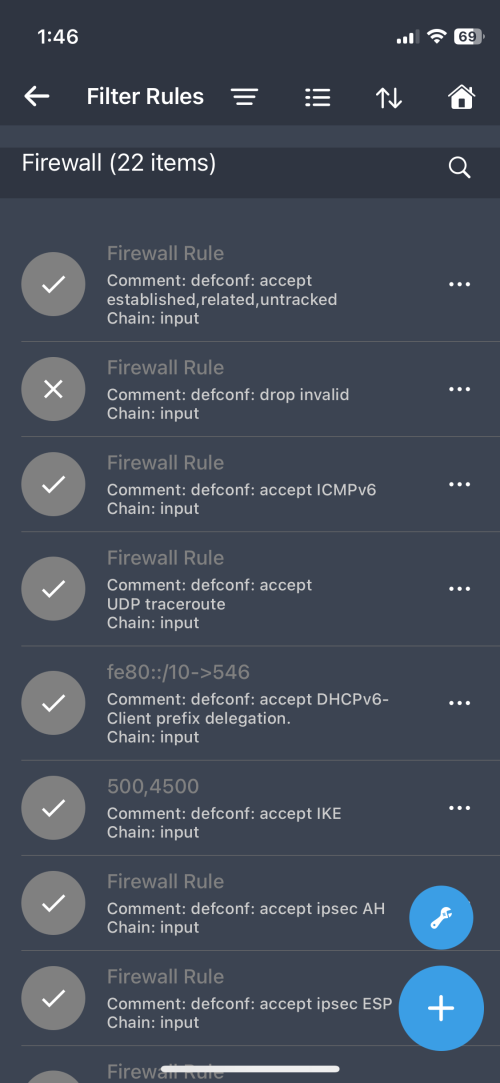
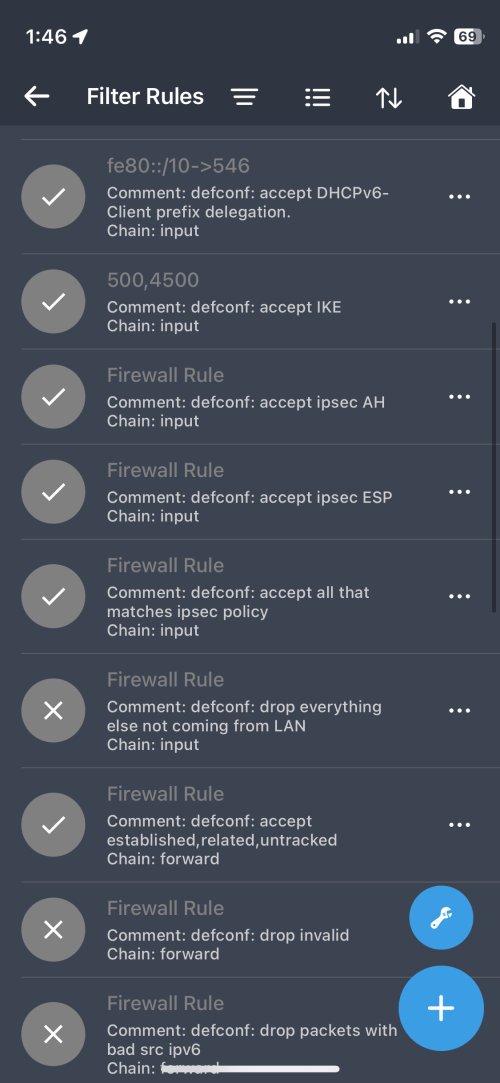
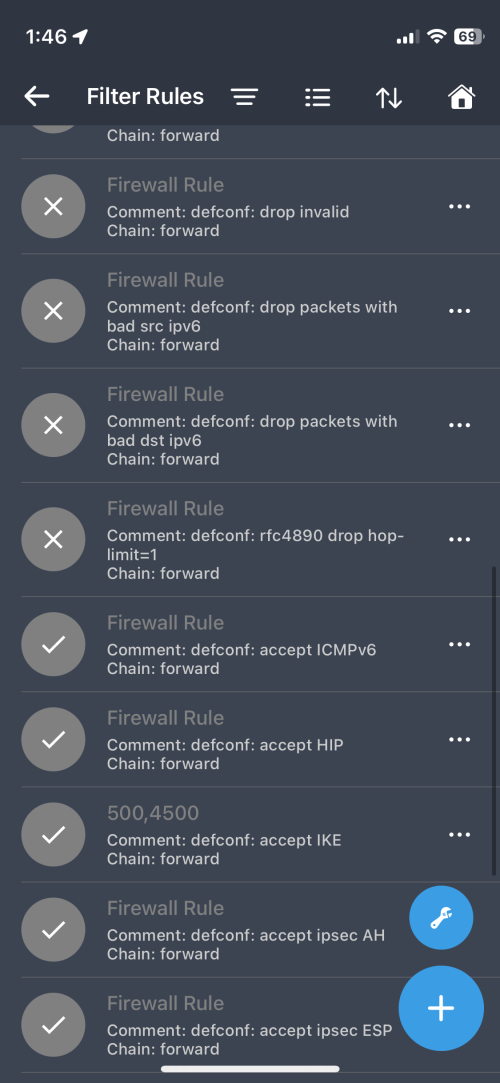
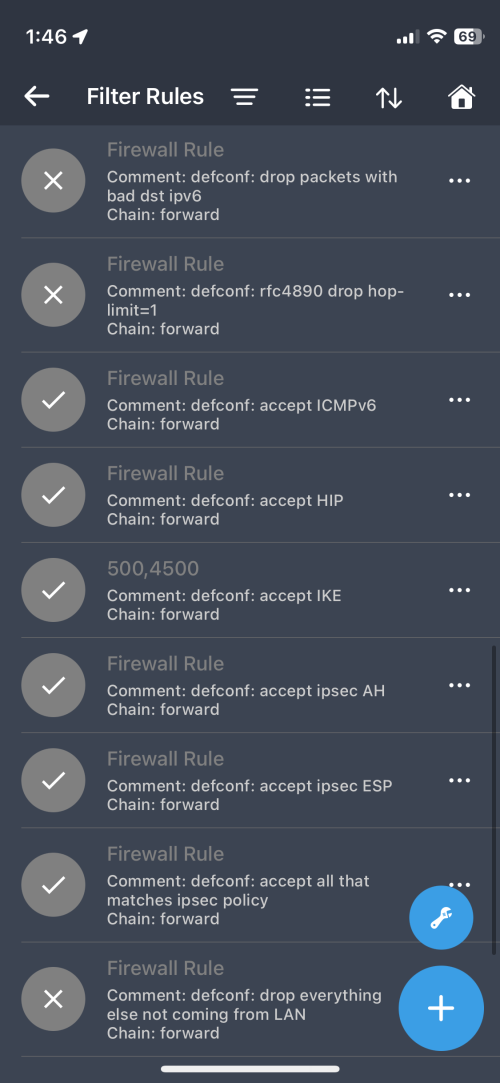
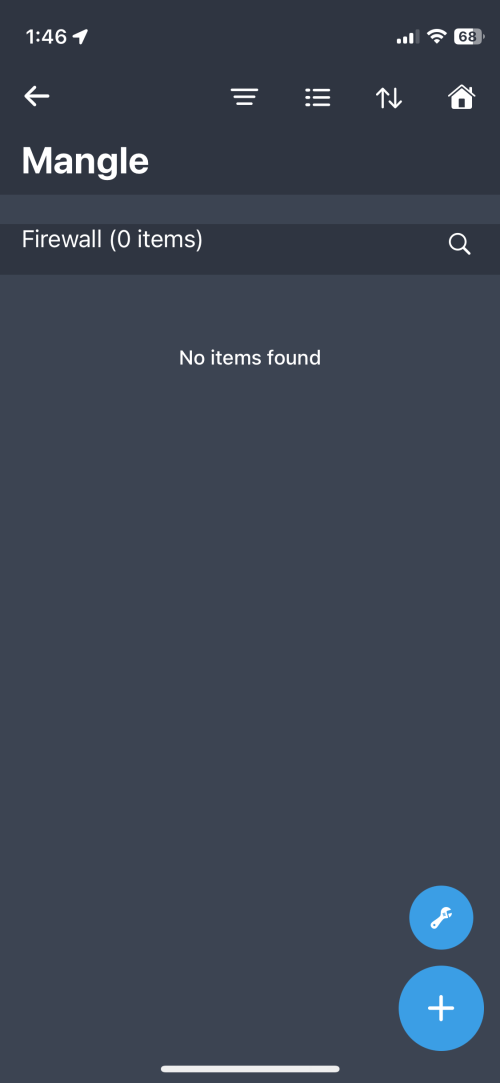
/ipv6 firewall filter
add action=accept chain=input comment="allow established and related" connection-state=established,related
This rule did it. Not sure why you keep harping on iptable. How Mikrotik did it delivers what I described.
I did it for hyperscaler, not eyeball network. But I am sure the same method works with CGNAT, where they get their address via IPv4 as a service. CPE side continue as its with dual stack.
See, you quickly say my method don't work for you without any context, as if I don't know Steam don't work with NAT64 or XLAT464.
I glossed over because you are blaming one security issue on IPv6, plus you lie about Shodan.
So many IPv4 network get hacked everyday yet nobody call it the IPv4 problem. Everything that showed up in Shodan is very well IPv4 problem, or is it?
When the term "IPv6" appear, suddenly it's all IPv6 fault.
Is it a Layer 3 protocol problem or is it a general security issue?
Don't tell me that you did not know that the firewall rule is just a wrapper for an iptables command, or ip6tables to be exact. That's why I mentioned iptables directly instead of routerOS firewall.
When I talk about Shodan, I am talking about client-level security in general, not IPv6 only to be exact. The devices you see in Shodan are all devices with lousy client-level security implementations, but you assume that all devices out there has stellar client-level security implementations, at least for IPv6. You rely too much on the hope that device manufacturers will implement robust security on their IPv6-supporting devices, but not all will do so, just like Sony.


 Jan 7 2024, 04:19 AM
Jan 7 2024, 04:19 AM

 Quote
Quote





 0.0166sec
0.0166sec
 0.62
0.62
 6 queries
6 queries
 GZIP Disabled
GZIP Disabled